The rise of blockchain technology has created an increasingly fragmented landscape. Dozens of independent networks, each with its own rules, tokens, and communities, operate in isolation by default. This makes it difficult for users to move assets or interact with applications across different chains without going through centralized exchanges. Cross-chain bridge crypto solutions have emerged as one of the most important infrastructure layers in the decentralized finance ecosystem, enabling direct asset transfers between blockchains without middlemen.
But bridges are not without controversy. Several of the largest crypto hacks in history have targeted cross-chain bridge protocols, exposing billions of dollars in losses. Understanding how these systems work, where they are vulnerable, and how to use them safely is essential for any serious crypto trader or DeFi participant. This guide breaks down everything you need to know about cross-chain bridges, from the mechanics to the risks to the practical steps for safer usage.
1. What Is a Cross-Chain Bridge in Crypto
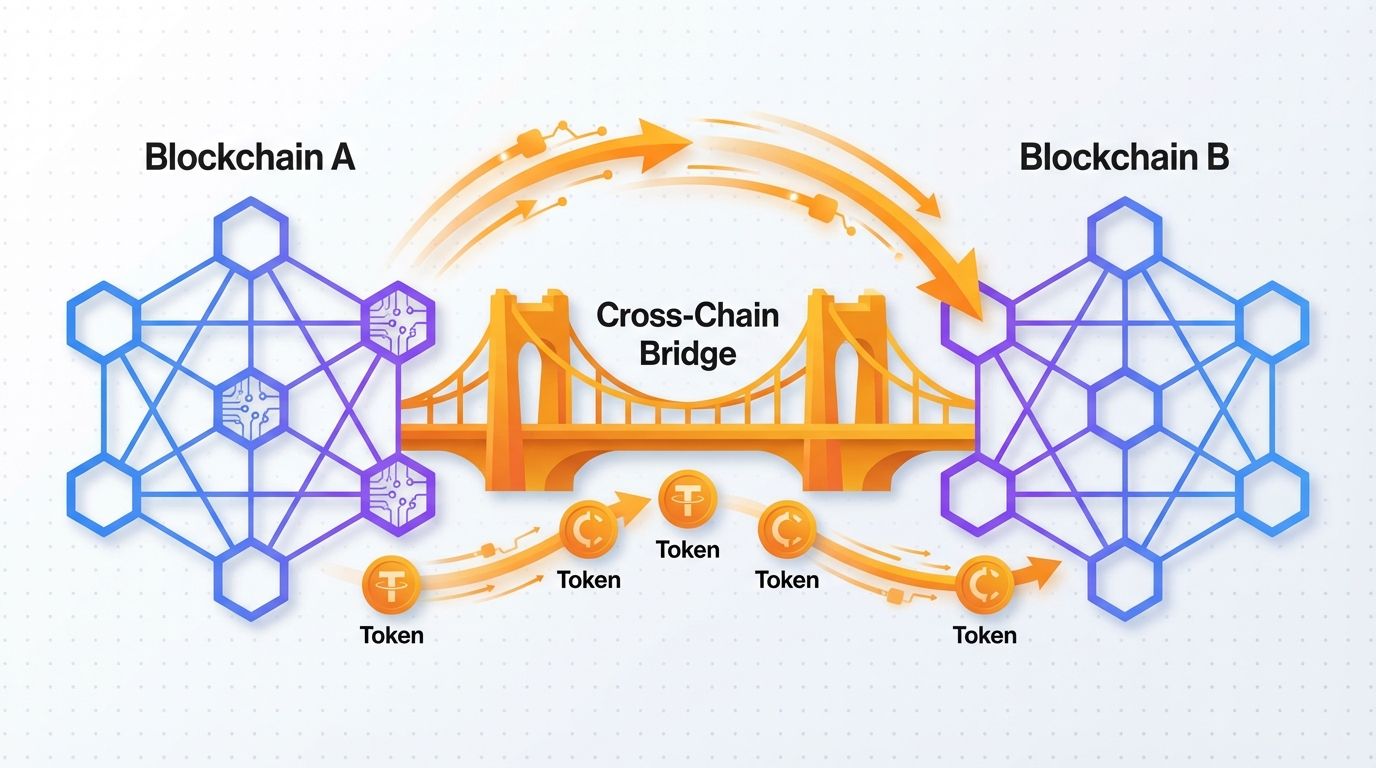
A cross-chain bridge is a protocol that allows users to transfer assets, data, or messages from one blockchain network to another. Because blockchains like Ethereum, Solana, and BNB Chain are designed as closed systems, they cannot natively communicate with each other. A cross-chain bridge acts as a connector between these isolated networks.
The most common use case is moving tokens. If you hold ETH on Ethereum but want to use it in a DeFi application on Avalanche, a bridge lets you move a representation of that ETH to the Avalanche network. The result is a "wrapped" or "bridged" version of the original token, which carries the same value but exists natively on the destination chain.
Cross-chain bridges come in several forms:
- Token bridges: Transfer specific tokens between chains
- General message bridges: Pass arbitrary data or smart contract calls across chains
- Liquidity bridges: Use pooled liquidity on both sides to facilitate instant swaps
Bridges are foundational to the concept of a multichain ecosystem. Without them, each blockchain is effectively a walled garden, limiting the composability and capital efficiency that makes DeFi so powerful.
2. How Cross-Chain Bridges Work
The mechanics behind cross-chain bridges vary by design, but most rely on one of a few core approaches. Understanding how these systems function helps you evaluate their trade-offs and risks.
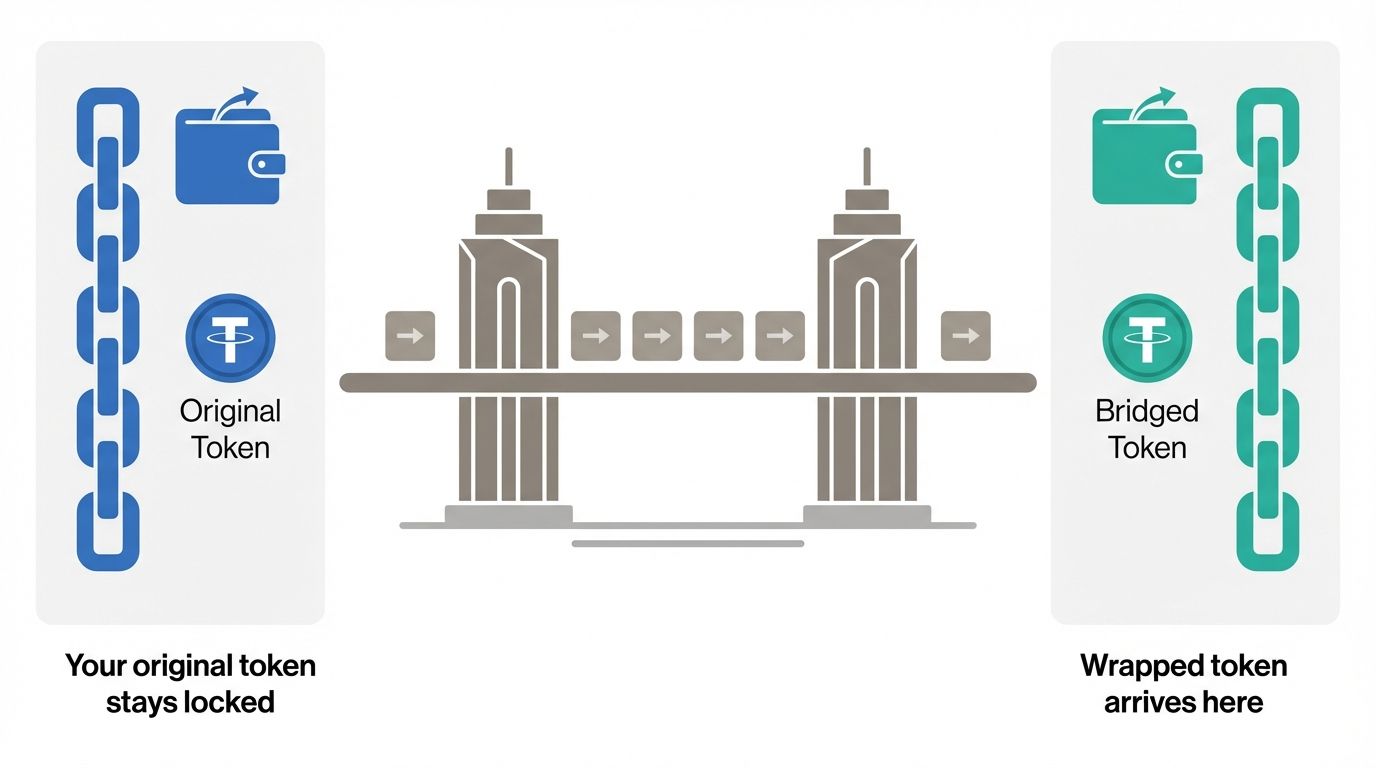
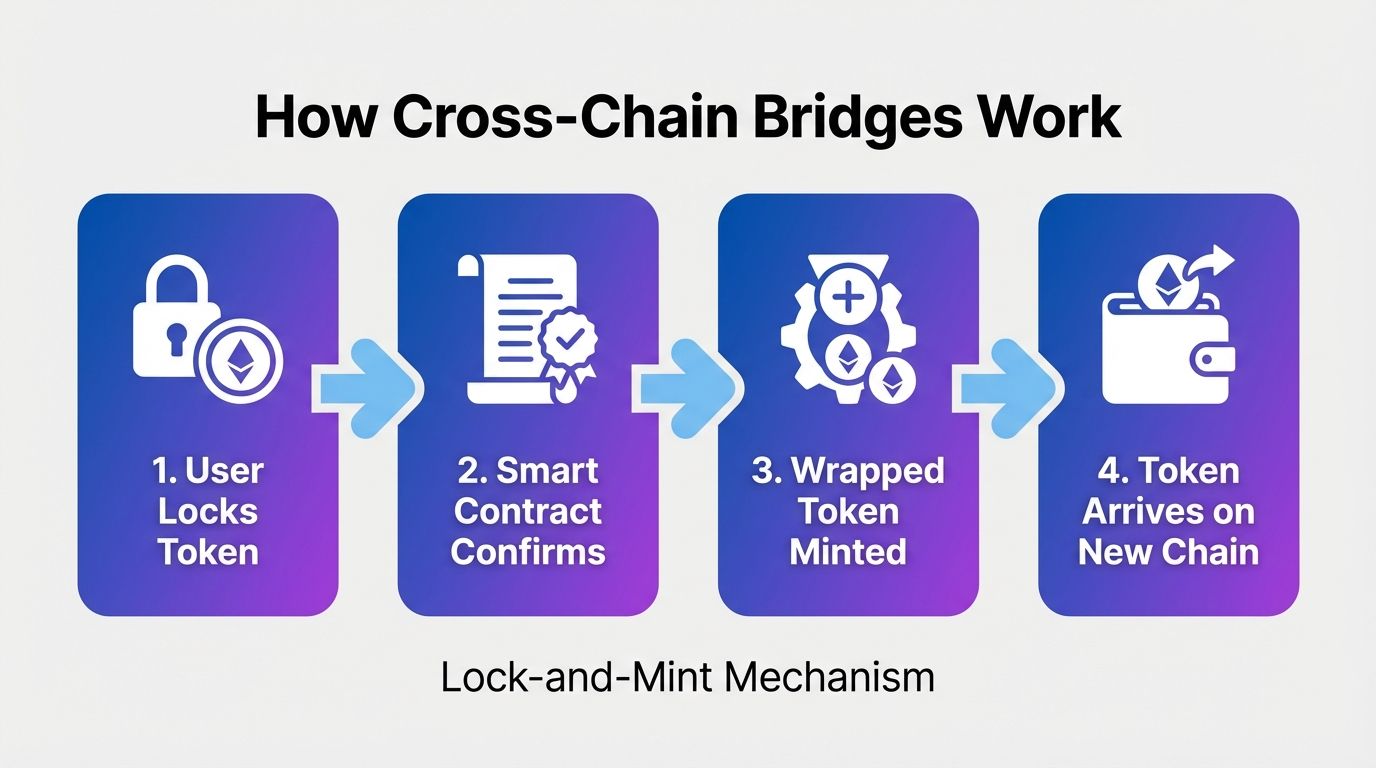
Lock-and-Mint
The most widely used model. When you send a token to a bridge, the protocol locks your original token in a smart contract on the source chain and mints a wrapped equivalent on the destination chain. When you want to return, you burn the wrapped token, and the original is unlocked and sent back. The locked tokens on the source chain serve as collateral backing all the wrapped tokens in circulation.
Burn-and-Mint
Some protocols use a native cross-chain token design. Instead of locking, the token is destroyed (burned) on the source chain and a new identical token is created (minted) on the destination chain. This is only possible when the token issuer controls the minting contract on both chains.
Liquidity Pool Model
Bridges using liquidity pools do not mint or lock tokens. Instead, liquidity providers deposit tokens on both sides of the bridge. When you bridge an asset, you deposit into the pool on one side and withdraw from the pool on the other. This model enables faster transfers and avoids the minting risk but depends on sufficient pool liquidity to function smoothly.
Optimistic Verification
Some bridges use an optimistic model where transactions are assumed valid by default and only challenged if a validator submits a fraud proof. This reduces costs but introduces a withdrawal delay, typically 7 days, to allow time for disputes.
Zero-Knowledge Proof Bridges
The most cryptographically secure approach uses zero-knowledge proofs to verify the state of one chain to another. ZK bridges can be trustless and fast but are computationally expensive to generate and currently more limited in deployment.
3. Major Types of Cross-Chain Bridges
Not all bridges are built the same. The crypto ecosystem has developed several distinct categories of bridges, each with different trust models, speeds, and supported chains.
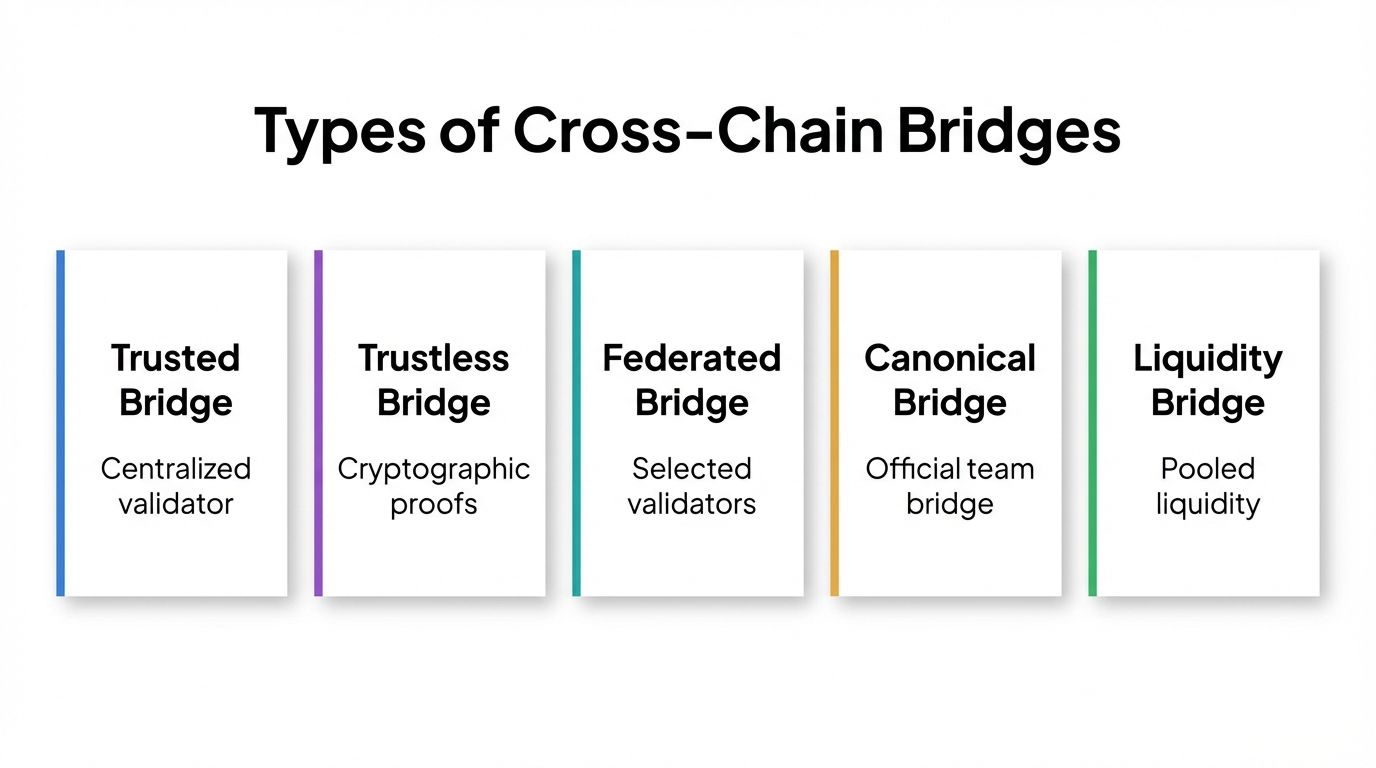
Trusted (Centralized) Bridges
These rely on a central operator or a small set of validators to confirm and process cross-chain transfers. They tend to be faster and cheaper but require users to trust a third party. If the operator is compromised or acts maliciously, user funds are at risk.
Trustless (Decentralized) Bridges
Trustless bridges rely on smart contracts and cryptographic proofs rather than human validators. They eliminate counterparty risk but can have higher gas costs and may be slower. Light client bridges and ZK bridges fall into this category.
Federated Bridges
A middle ground between fully centralized and fully trustless. A federation of validators, typically selected through staking or governance, must reach consensus before approving a transfer. The security depends on the size and decentralization of the validator set.
Canonical vs. Third-Party Bridges
Canonical bridges are officially deployed by the blockchain's core team. Third-party bridges are built by independent protocols and often support more chains and tokens. Third-party bridges sometimes offer faster withdrawals or better rates but carry additional smart contract risk.
Cross-Chain DEX Aggregators
Some protocols combine bridging with decentralized exchange routing. They find the most efficient path to move your asset, potentially swapping it along the way. This category has grown rapidly and often provides a better user experience than standalone bridges.
4. Risks and Security: The History of Bridge Hacks
Cross-chain bridges have become one of the most targeted attack surfaces in all of crypto. The reason is simple: bridges often hold large concentrations of locked assets, making them high-value targets. A single smart contract vulnerability can expose the entire liquidity pool or collateral vault.
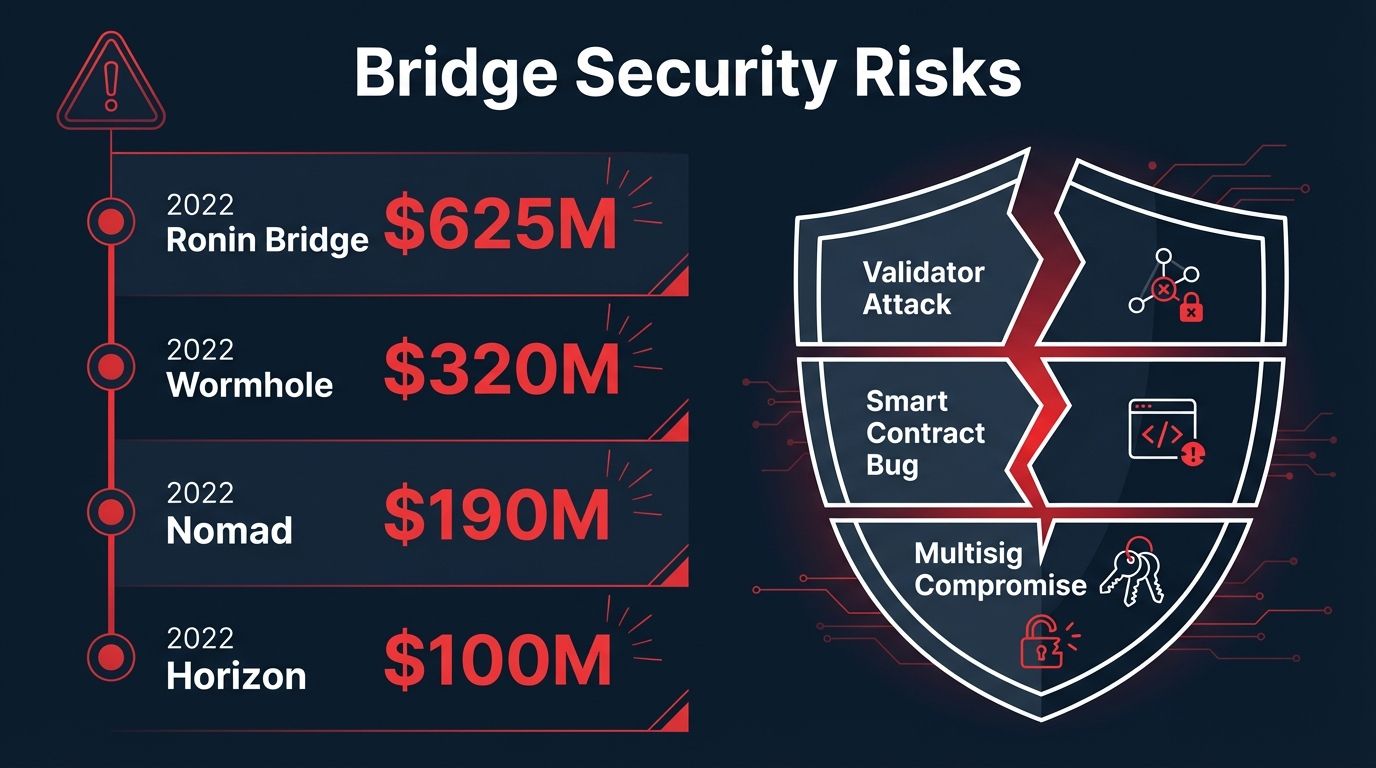
Some of the most significant bridge exploits on record include:
- Ronin Bridge (2022): Attackers compromised validator private keys, draining approximately $625 million in ETH and USDC. This remains one of the largest single crypto hacks in history.
- Wormhole Bridge (2022): A signature verification bug allowed an attacker to mint 120,000 wrapped ETH without providing any collateral, resulting in a $320 million loss.
- Nomad Bridge (2022): A flawed initialization in a smart contract update allowed anyone to spoof messages and drain funds. Over $190 million was taken in a chaotic free-for-all.
- Harmony Horizon Bridge (2022): Compromise of two out of five multisig keys was enough to drain $100 million from the bridge.
These incidents reveal structural weaknesses common to many bridge designs:
- Excessive reliance on small validator sets or multisig wallets with few signers
- Concentrated liquidity creating large single-point-of-failure targets
- Complex cross-chain message verification logic prone to edge-case bugs
- Rushed deployments without sufficient auditing
The total losses from bridge exploits across 2021 and 2022 exceeded $2 billion, prompting the industry to push toward more robust ZK-based verification and stricter audit standards. Despite improvements, bridge security remains an evolving challenge.
5. How to Use a Cross-Chain Bridge Safely: Step-by-Step
Bridging is a powerful tool, but it should be approached with care. Following a consistent process significantly reduces the risk of losing funds to scams, bugs, or user error.
- Verify the official bridge URL. Phishing sites mimicking popular bridges are common. Always navigate to the protocol's URL from an official source, such as the project's verified social media profile or a trusted directory. Never use links from DMs or search ads without cross-checking.
- Check bridge audits and security track record. Before using a bridge, look up whether the smart contracts have been audited by reputable firms. Check whether the bridge has been previously exploited. A clean audit history is not a guarantee but is a positive signal.
- Start with a small test transaction. Before sending significant value, send a small test amount first. Confirm the funds arrive correctly on the destination chain before proceeding with the full transfer.
- Keep enough gas on the destination chain. Some bridges require you to pay gas on the destination chain to claim your funds. Make sure you have enough native token on the receiving chain before initiating the transfer.
- Understand the expected transfer time. Bridges can take anywhere from seconds to 7 days, depending on the mechanism used. Do not be alarmed if your funds do not arrive instantly, but do check the expected window before you send.
- Never bridge more than you need. Avoid leaving large sums in a bridge or in a wrapped token form longer than necessary. Minimize your exposure window by bridging only what you plan to use promptly.
- Use wallets with separate bridging allowances. Consider using a dedicated wallet for DeFi and bridging activities, separate from your long-term cold storage. This limits the blast radius of a compromised approval or interaction.
- Track your transaction on both chain explorers. Most bridges provide a transaction hash. Use it to monitor progress on both the source and destination chain explorers to catch any issues early.
6. Managing Your Bridged Assets with Altrady
Once you have bridged assets across chains, tracking your positions across multiple networks can get complex quickly. Altrady is a professional crypto trading platform that brings together portfolio management, real-time market data, and automated trading tools in one dashboard. Whether you are managing wrapped tokens on multiple chains, rebalancing DeFi positions, or executing trades after bridging, Altrady gives you the visibility and control you need.
Altrady supports connections to major exchanges and provides portfolio tracking across your holdings, helping you stay organized in a multichain world. The platform is built for active traders who need speed, accuracy, and reliability when markets move fast.
Ready to streamline how you manage your crypto across chains? Start your free trial with Altrady today and experience professional-grade trading tools without the complexity.
Frequently Asked Questions
What is the difference between a cross-chain bridge and a centralized exchange?
A centralized exchange (CEX) is a custodial service where you deposit funds and the exchange holds them on your behalf. When you move assets between chains on a CEX, the exchange handles everything internally. A cross-chain bridge is a non-custodial protocol where your wallet interacts directly with smart contracts. Bridges give you more control and privacy, but they require you to manage the transaction yourself and carry smart contract risk.
Are cross-chain bridges safe to use?
The safety of a bridge depends on its design, the quality of its smart contract audits, and the size of its validator set or security infrastructure. No bridge is completely risk-free. ZK-based bridges and those with large, decentralized validator sets are generally considered more secure than small multisig setups. The best practice is to use well-audited, established bridges, start with small amounts, and avoid leaving funds in bridged form for extended periods.
How long does a cross-chain bridge transfer take?
Transfer times vary significantly by bridge type. Liquidity pool bridges and some lock-and-mint bridges can complete transfers in minutes or even seconds. Optimistic rollup bridges typically impose a 7-day delay on withdrawals back to Ethereum mainnet. Always check the expected transfer time before initiating a bridge transaction, especially if you are working against a trading deadline.
What happens if my bridge transaction gets stuck?
A stuck bridge transaction usually means the transaction is waiting for additional block confirmations, experiencing network congestion, or has encountered an issue with the relayer. Most bridge protocols have a support page or community channel where you can submit your transaction hash to get help. In some cases you may need to manually claim funds on the destination chain using the bridge interface.
Can I bridge any token to any blockchain?
Not every token is supported on every bridge. Each bridge has its own list of supported assets and destination chains. Some tokens only have liquidity on one or two chains, and bridging an obscure token may result in poor rates or unavailable routes. Cross-chain DEX aggregators often give you better coverage by routing through multiple bridges and swap paths to find the best available option for your specific token and destination.