You have heard "smart contract" hundreds of times - in DeFi protocols, NFT mints, liquidations, governance votes - but you still hesitate when someone asks what one actually does to your money when you click Approve. As a trader, you do not care that a contract is written in Solidity or Rust. You care that the contract holds your collateral, executes your liquidation, controls your withdrawal, or rugs your tokens.
Smart contracts only make sense in the context of what is blockchain (the ledger they live on) and what is DeFi (the most common environment where they execute against your capital).
This guide treats smart contracts the way an experienced trader thinks about them: as counterparties with a specific set of rules, a verifiable history, and a measurable risk profile. By the end, you should be able to glance at a contract you are about to use and form a quick, defensible view on whether the trade is worth the operational risk.
What a Smart Contract Actually Does

A smart contract is a program deployed to a blockchain that holds state, accepts transactions, and executes logic according to its code. Once deployed, it operates autonomously. The same input produces the same output every time. Nobody (in a properly designed contract) can stop it, refund you, or change the terms after the fact.
For a trader, the practical implications are concrete. When you swap on Uniswap, a smart contract takes your tokens, runs the price formula, sends you the output tokens, and updates the pool's state. When you supply USDC to Aave, the contract holds your deposit, mints aTokens that represent your claim, and tracks accrued interest. When you open a leveraged position on a perp DEX, the contract debits your collateral, computes funding, and triggers liquidation if your margin breaks.
A contract is not "smart" in the AI sense. It is just code that runs deterministically. The intelligence, or stupidity, was put there by the developer. The number of contracts that have lost user funds because of a missing semicolon or a forgotten access control check should convince you that "smart" is marketing, not engineering.
The Trader's Mental Model: Code as Counterparty
Treat every smart contract you interact with as a counterparty whose contract terms you cannot renegotiate. The terms are the source code. The risk is what that code does in cases the developer did not anticipate.
When you trade on a regulated futures exchange, your counterparty risk is mediated by the clearinghouse, the exchange's reserves, and the legal system. When you trade on a DEX, your counterparty is the contract. Its only obligation is to do exactly what it is programmed to do. There is no insurance fund unless the protocol explicitly built one, and no court that can claw back stolen funds.
This changes how you size positions and choose protocols. A sensible DeFi user does not deposit their full stack into a six-month-old protocol with one audit and a 50 million dollar TVL. Match exposure to the contract's track record, not the headline yield.
"The protocol" and "the contract" are often the same thing. When you give Uniswap a token approval, you are not approving Uniswap Labs, you are approving a specific contract address. If the front-end is hijacked and points elsewhere, the original approval is still valid. Always check what you are signing.
Where You're Already Using Smart Contracts

Almost every on-chain action a trader takes is a smart contract interaction. A short tour:
DEX swaps and routing. Uniswap, Curve, Balancer, and PancakeSwap each consist of a router contract that sits in front of a network of pool contracts. Aggregators like 1inch, Cowswap, Jupiter, and Matcha add another contract layer that splits orders across multiple venues. Each interaction involves at least two or three contract calls.
Lending markets. Aave, Compound, Morpho, and Spark are systems of contracts: a pool that holds reserves, a price oracle, a liquidation contract, and an interest rate model. When you supply or borrow, your transaction touches several of these.
Perpetual futures and options. Hyperliquid, GMX, dYdX, Synthetix, and Lyra rely on collateral vaults, position managers, oracle adapters, and funding rate calculators. The interactions are abstracted away by the front-end, but the risk lives in those contracts.
Staking and liquid staking. Lido, Rocket Pool, EigenLayer, Jito, and Marinade all run on contracts that handle deposits, validator delegation, and reward distribution. LSTs and LRTs are tokens issued by these contracts.
NFTs and tokenization. Every ERC-721 and ERC-1155 contract is a smart contract. The marketplaces (OpenSea, Blur, Magic Eden) run on yet more contracts that hold escrow during sales, distribute royalties, and resolve auctions.
If you have ever signed a transaction in MetaMask or Phantom, you have already trusted multiple contracts with real value. The goal is to start being deliberate about which ones earn that trust.
The Big Risks: Bugs, Exploits, Rug Pulls, Governance Attacks

Smart contract risk is not a single category. It is a family of distinct failure modes, each with its own pattern and its own historical examples.
Logic bugs and exploits. A bug in the contract's logic that allows an attacker to drain funds. Examples include reentrancy attacks (the original DAO hack in 2016), oracle manipulation (numerous flash-loan exploits), and rounding errors (smaller but recurring). The Curve Finance Vyper compiler bug in 2023 drained pools because of a flaw in the language itself, not the protocol code. The lesson: even high-quality teams ship bugs.
Economic exploits. The contract works as designed, but the design has a flaw an attacker can profit from. Mango Markets in 2022 was drained for 117 million dollars because a trader manipulated the price oracle to inflate collateral value, then borrowed against it. The contract did exactly what it was told to do. The design was the problem.
Rug pulls. The deployer holds privileged access (mint, pause, withdraw functions) and uses it to drain user funds or dump tokens. Most common in low-cap memecoins and unaudited yield farms. Telltale signs include unverified contracts, unrenounced ownership, and large premints in deployer wallets.
Governance attacks. The protocol is controlled by token holders, and an attacker accumulates enough voting power to pass a malicious proposal. Beanstalk in 2022 was drained for 182 million dollars when an attacker used a flash loan to acquire majority voting power and pass a proposal that transferred funds to themselves.
Frontend and wallet attacks. The contract is fine, but the user-facing site or wallet integration is compromised. Curve's website was DNS-hijacked in 2022. Multiple wallet providers have been targeted. From the user's perspective, the result (signed transaction, lost funds) is identical to a contract exploit.
Approval drains. You give a contract permission to spend your tokens, the contract or front-end is later compromised, and an attacker uses the approval to transfer your tokens. Periodically auditing and revoking unused approvals at revoke.cash is one of the highest-leverage habits in DeFi.
How to Evaluate Smart Contract Risk in 5 Minutes
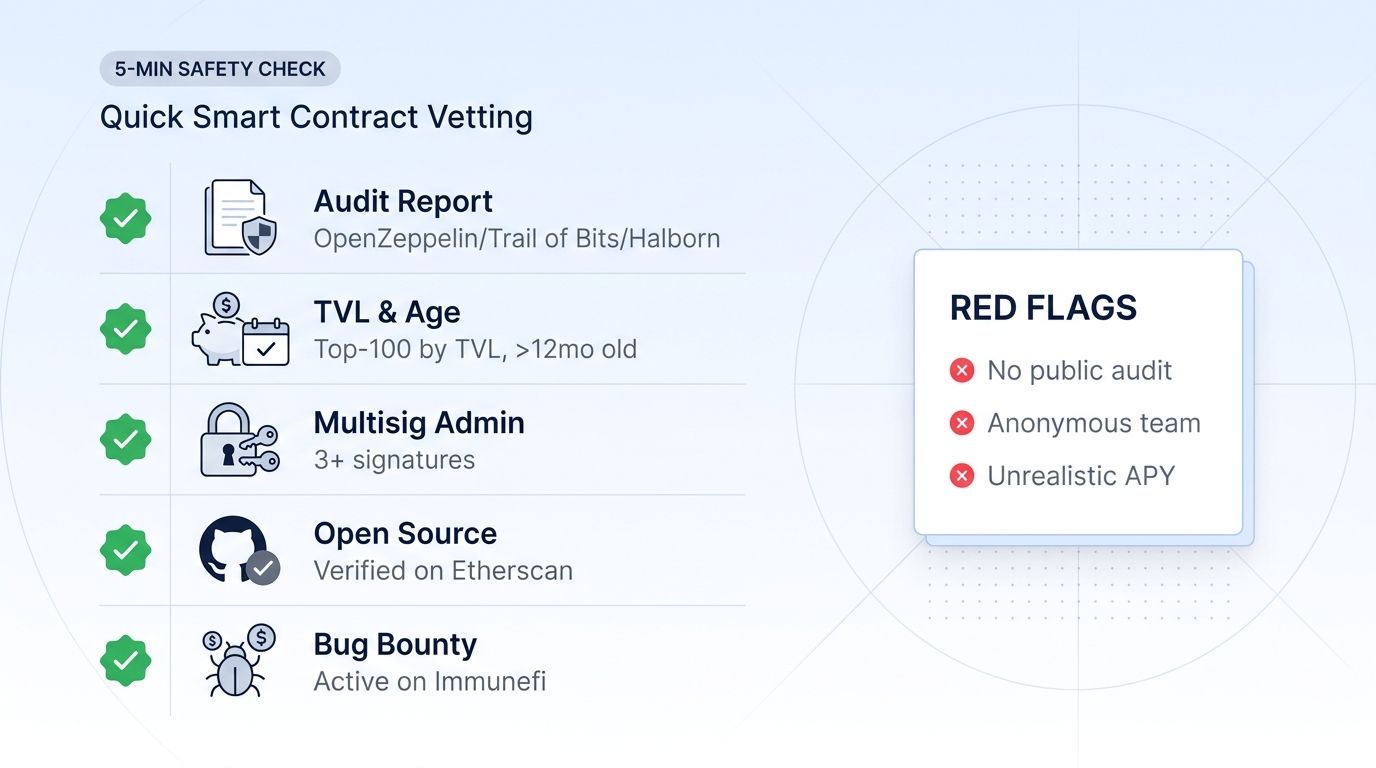
A practical, repeatable checklist before you deposit funds into any contract.
Check the audit reports. Quality auditors like Trail of Bits, OpenZeppelin, ChainSecurity, Spearbit, and Code4rena publish detailed reports. One audit is the minimum. Two or more by independent firms is a meaningfully better signal. No audit is an immediate no for anything beyond a tiny test position.
Check the age and TVL. A contract that has held nine figures of TVL for two-plus years has been a target for the best whitehats and blackhats in the industry. Survivorship is a meaningful signal, even if it is not proof. New contracts deserve smaller positions until they accumulate that history.
Check the multisig and admin keys. Who can upgrade the contract or pause it? A multisig with reputable signers is acceptable. A single externally owned account (EOA) with admin power is a major red flag. A timelock on upgrades (typically 24 to 72 hours) gives users time to exit before changes take effect.
Check the source code. It does not have to be line by line. Look for: is the contract verified on Etherscan or Solscan, do the deployer wallets hold an outsized share of the supply, does the contract have mint, pause, or backdoor withdrawal functions. DeFiSafety, DefiLlama's audit pages, and protocol-specific docs make this much faster than reading raw Solidity.
Check current bug bounties. Active programs on Immunefi, Code4rena Continuous, or Hats Finance with payouts in the high six or seven figures show that the team takes security seriously and has economic incentives aligned for whitehats.
You do not need to be a smart contract auditor. You need to ask the same questions a credit analyst asks before extending a loan. The contract's track record, governance, and transparency are your collateral analysis.
Famous Smart Contract Exploits Traders Should Remember
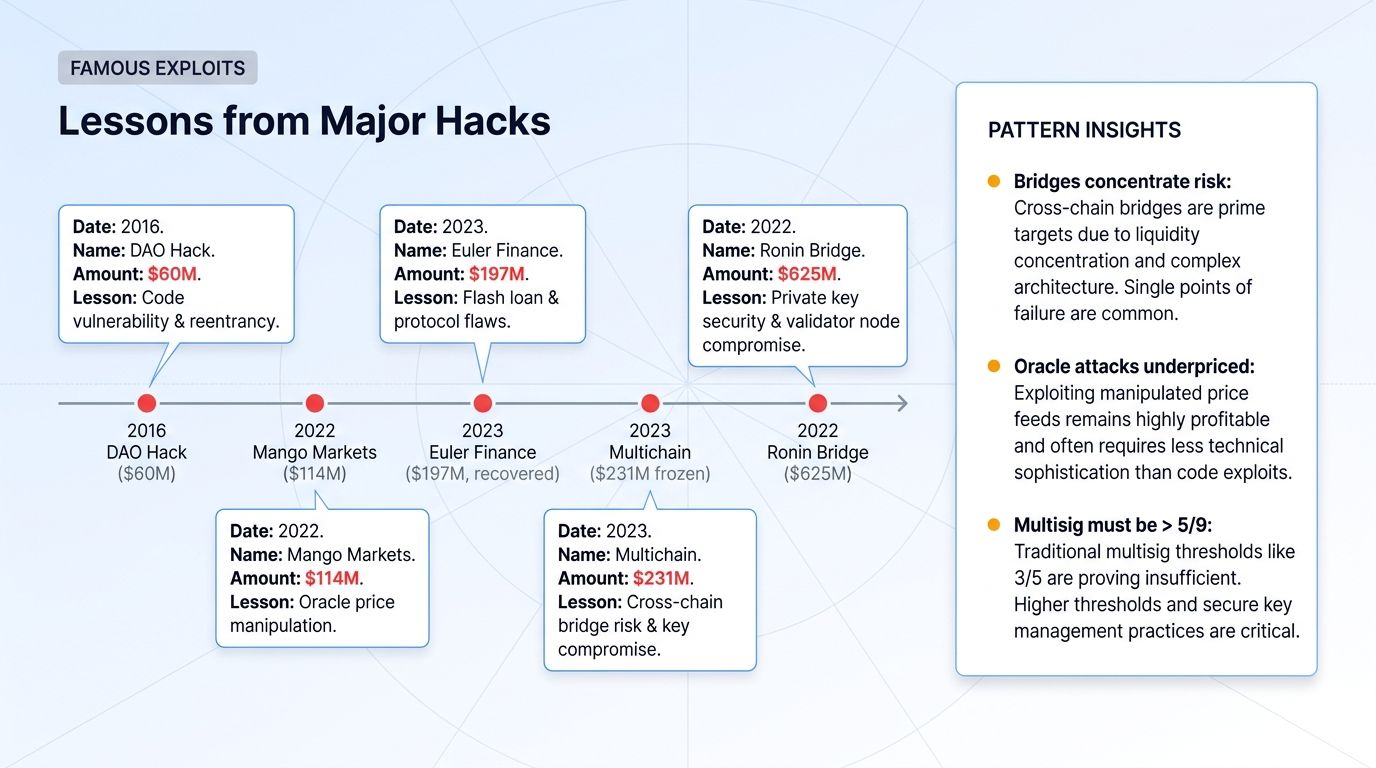
History does not repeat exactly, but the patterns do. A few exploits worth keeping in mind:
The DAO hack (2016). A reentrancy bug drained 3.6 million ETH from one of the earliest major DeFi protocols. The Ethereum community responded with a hard fork that restored the funds, splitting the chain into ETH and ETC. This event shaped Ethereum's culture around immutability and security.
Mango Markets (2022). Avraham Eisenberg manipulated the price of MNGO via a thin order book on a centralized exchange to inflate collateral on Mango, then borrowed 117 million dollars against it. The aftermath set legal precedent: he was later convicted of market manipulation.
Curve Finance (2023). A bug in older versions of the Vyper compiler allowed reentrancy attacks against several Curve pools, draining roughly 70 million dollars before whitehats and the team contained it. The protocol code itself was not at fault, the language compiler was.
Euler Finance (2023). A donate-and-liquidate exploit drained 197 million dollars despite multiple audits. Most of the funds were eventually returned by the attacker, but the incident remains a lesson in audit limits.
Multichain bridge collapse (2023). Roughly 1.5 billion dollars in user assets became inaccessible when the project's CEO was reportedly detained and admin keys went offline. The exploit was not a bug but a centralization failure dressed in DeFi clothing.
Ronin bridge (2022). North Korean actors compromised five of nine validator keys and drained 625 million dollars. The lesson: bridge security depends on the validator set, and small validator sets concentrate risk.
The common thread: every loss had warning signs that were visible before the fact. Centralized admin keys, thin oracles, unaudited dependencies, low validator counts, novel mechanisms without battle-testing. Pattern matching against past exploits is one of the most useful skills in DeFi.
FAQ
Are smart contracts the same as blockchain?
No. The blockchain is the underlying ledger that records transactions. Smart contracts are programs that run on top of certain blockchains (Ethereum, Solana, and most other programmable chains). Bitcoin's base layer has only very limited scripting, which is why most smart contract activity lives on Ethereum and its peers.
Can a smart contract be changed after deployment?
By default no, the deployed bytecode is immutable. But many protocols use proxy patterns, where the contract you interact with delegates to an implementation contract that can be upgraded by an admin or DAO. Always check whether the contract you are using is upgradeable, who can upgrade it, and whether there is a timelock.
Do audits guarantee a contract is safe?
No. Audits reduce the chance of a bug being missed but do not eliminate it. Multiple audited protocols have been exploited. Treat audits as one input among many: track record, TVL, governance, bug bounties, and code transparency all factor in.
Why do approvals matter so much?
When you grant a token approval, you are giving a contract permission to move your tokens up to a specified amount. If that contract is later exploited, or you signed an approval to a malicious contract, the attacker can move your tokens without further interaction from you. Use revoke.cash periodically to audit and remove unused approvals, and prefer wallets like Rabby that show approval requests in human-readable form.
Can I get my money back after a smart contract exploit?
Sometimes, rarely. A small number of cases have ended in attacker negotiations and partial returns (Euler is the most famous). Some protocols have insurance funds or DAO-funded compensation programs. The honest answer is: if a contract drains your funds, plan for the loss to be permanent and treat any recovery as upside.
Final Thoughts
Smart contracts are the infrastructure of modern crypto trading. Every DEX swap, every lending position, every NFT mint, every staked asset is mediated by code that you have implicitly accepted as your counterparty. Understanding this changes how you size positions, choose protocols, and manage approvals.
The traders who avoid catastrophic on-chain losses are not the ones with the deepest technical knowledge. They are the ones with the most disciplined processes: small positions in new protocols, audits and TVL as inputs, regular approval audits, and a baseline assumption that any contract can fail. That mindset costs nothing and saves accounts.
Once you have your on-chain risk management dialed in, the next question is execution across both DeFi and centralized venues. Altrady gives you a single multi-exchange terminal, smart trading tools, paper trading to test strategies risk-free, and a clean workflow that lets you focus on positioning rather than juggling tabs. Try Altrady free and bring the same discipline to your CEX execution that you already apply to your smart contract counterparties.